Articles on Security

Visitor Management Integration with Access Control Systems
Integrating visitor management with access control automates guest entry by syncing digital check-ins with physical security hardware. This process replaces manual logbooks with temporary digital credentials, ensuring only authorized visitors can enter specific office zones while creating an audit-ready data trail for compliance.
By Nathanial Sterling

Visitor Management Best Practices for Security and Compliance
Effective visitor management requires more than a digital guestbook. This guide covers how to enforce security protocols, maintain compliance through audit-grade data, and integrate visitor workflows into your broader workplace operations. Learn how to automate check-ins and legal document signing to reduce front-desk friction while maintaining strict security standards.
By Oliver Wright

How to Create a Professional Visitor Check-In Experience
A professional visitor check-in experience secures your facility while providing a high-quality first impression. By moving beyond manual logs to a unified operational system, organizations can enforce security policies, automate host notifications, and capture audit-grade data on every person entering the workplace. This guide explains how to implement visitor management that prioritizes operational truth over simple registration.
By Julian Everett

Data Privacy in the Modern Workplace
In today's digital workplace, data privacy has become a critical concern for organizations of all sizes. This article explores the fundamentals of data privacy, why it matters for your business, key regulations to be aware of, and practical strategies for implementing robust privacy practices that protect your organization while building trust with employees and customers.
By Julian Everett

Blockchain Technology: Revolutionizing Workplace Management
Blockchain technology is reshaping how organizations manage their workplace operations. This article explores how decentralized ledger technology provides unprecedented security, transparency, and efficiency for corporate HR managers, IT departments, facility management teams, and educational institutions, with practical implementation strategies and real-world case studies.
By Ethan Montgomery
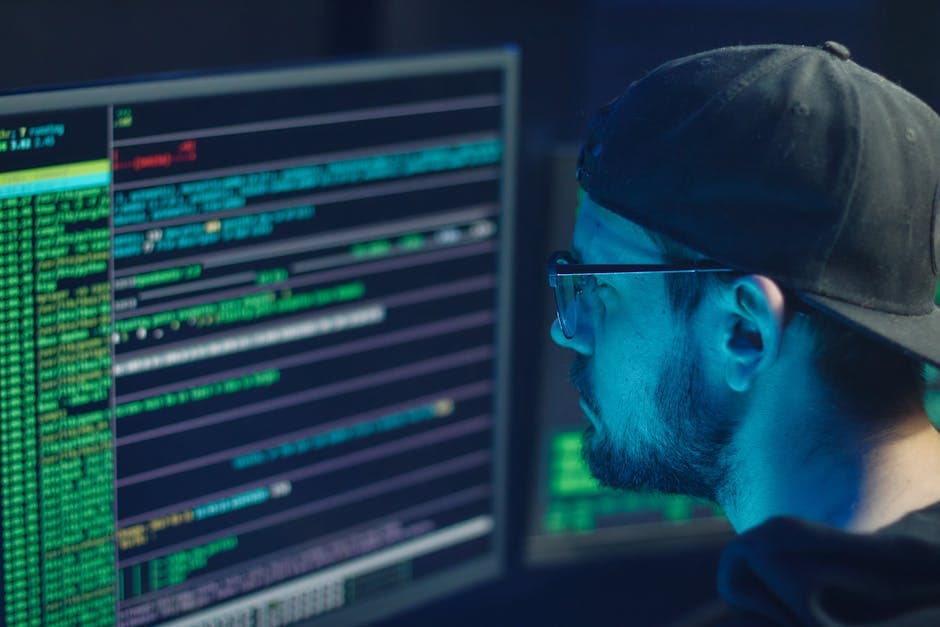
Strengthening Your Digital Fortress
In today's data-driven world, information security has become a critical concern for organizations of all sizes. This comprehensive guide explores the fundamental principles of InfoSec, key threats, essential protection strategies, and how to build a robust security framework that safeguards your most valuable digital assets.
By Nathanial Sterling

The Ultimate Guide to Access Control Systems for Modern
Access control systems form the backbone of modern workplace security, determining who can enter physical spaces and access digital resources. This comprehensive guide explores different types of access control solutions, implementation strategies, and best practices to help corporate security managers create safer, more efficient work environments while protecting sensitive information and assets.
By Alexander Bennett

Mastering Incident Response: A Guide for Cybersecurity Teams
In today's threat landscape, having a robust incident response plan is no longer optional but essential. This comprehensive guide explores the fundamentals of incident response, from building effective teams to implementing frameworks that minimize damage and recovery time. Discover how proper preparation can significantly reduce breach costs and protect your organization's critical assets.
By Lucas Hamilton

Mastering Threat Detection: Essential Strategies for Modern
In today's digital landscape, organizations face increasingly sophisticated cyber threats. This comprehensive guide explores modern threat detection approaches, implementation strategies, and how integrating advanced security measures can protect your workplace from evolving threats while maintaining operational efficiency.
By Charlotte Reed

Enhancing Workplace Security: The Complete Guide to Video
In today's security-conscious business environment, video surveillance systems have evolved beyond simple monitoring tools into comprehensive security solutions. This guide explores how modern surveillance technology can enhance workplace security, protect valuable assets, and provide actionable insights while addressing privacy concerns and compliance requirements for corporate environments.
By Sophia Marshall
Effective Risk Management Strategies for Modern Businesses
In today's volatile business landscape, effective risk management is crucial for organizational resilience. This article explores comprehensive strategies for identifying, assessing, and mitigating various business risks, from cybersecurity threats to operational disruptions. Learn how to develop robust risk management frameworks that protect your assets while enabling sustainable growth.
By Evelyn Parker
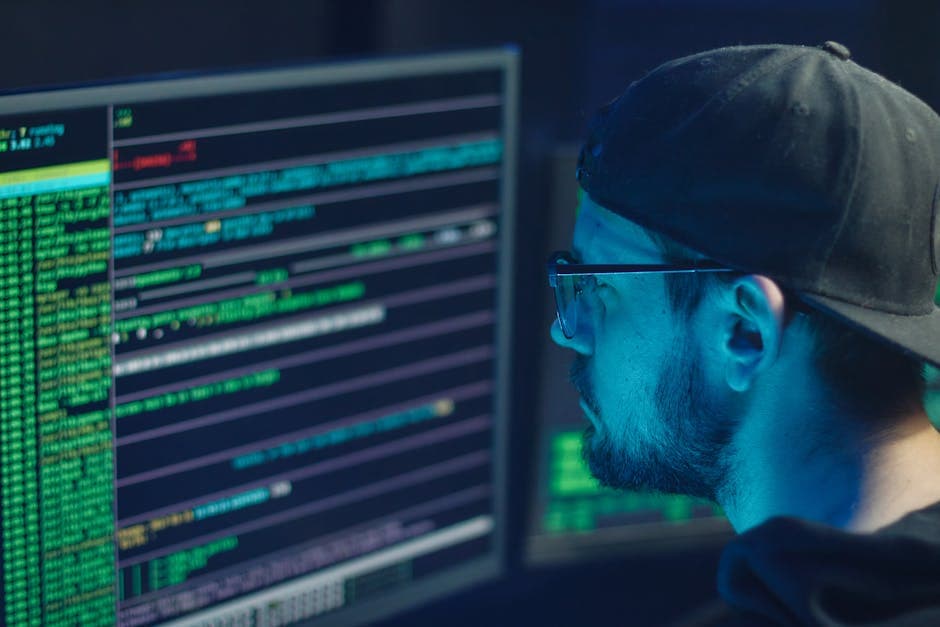
Strengthening Your Digital Fortress
In today's interconnected business environment, cybersecurity has become a critical priority for organizations of all sizes. This comprehensive guide explores essential cybersecurity practices, from implementing Zero Trust strategies to leveraging AI-powered security solutions, providing IT and facility managers with practical approaches to protect their digital assets against evolving threats.